Blog

What is Bluesnarfing?
Cybercriminals or hackers can access data on PC, laptops, mobiles, etc., with Bluetooth only. Did you know about this fact? When you are in any public space with your Bluetooth connection activated, people nearby can connect mobiles and download images from yours. It can happen to any person. While you see any Bluetooth-related activity on your mobile, ensure that anyone else is trying to make a bluesnarfing attack on you if you have not initiated your phone. This guide lets you know what it is and how you can prevent them.
What is Bluesnarfing?
Bluesnarfing is a hacking attack that needs a Bluetooth connection to work, through which hackers can steal data from a wireless device via Bluetooth connections. It happens on smartphones, computers, tablets, laptops, etc.
Hackers can take your contacts, images, messages, video, etc. Even they can extract your password from your device quickly. Usually, they search for devices with an active Bluetooth connection. After that, they use a scanning technique to detect blind spots in the object exchange protocol of mobiles. Thus, they can transmit data between your device and the device of the cyberattackers. Mostly, victims can’t realize that their device got hacked.
How Does Bluesnarfing Work?
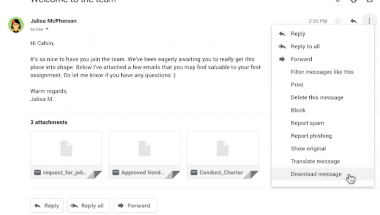
Hackers have to exploit OBEX or the object exchange protocol to begin attacks. Then, they use the technique to exchange information between wireless devices. In this case, the Bluediving tool can help you.
They pair their systems with a victim’s device. After that, they use lucrative tools to attack their target. If your device does not have powerful firmware protection, hackers can snatch data from it. They produce bluesnarfing tools themselves or buy these online. All the ready-to-use tools are available on the dark web.
How Can You Detect Bluesnarfing?
Your data is vital to you, and that is why it is essential to guard your device as you don’t know who wants to grab your data. Unfortunately, a few companies do the business of data mining.
Mostly, people encounter the problem with the default Bluetooth settings on most devices. In most cases, Bluetooth settings are available on the discovery mode in smartphones. Therefore, it becomes easier for hackers to access devices if they are within 30 feet of your mobile.
You must know that hackers can even make calls or send texts to your contacts. These attackers can also tarnish your image or defraud your contacts when they get your device. Therefore, you have to detect the attacks quickly to combat them immediately.
However, hackers can execute the attack using a laptop only, and without a laptop, they cannot run the operation. Cyberattackers generally connect a Bluetooth dongle and other tools to do it.
About Bluesnarfing:
It is an advanced form of cyberattack for which expert programmers can perform it only. They mainly steal data to sell these on the dark web. However, they are not only petty thieves; even famous tech companies may be involved in such activities.
For example, according to the New York Times, Google stole multiple information in 2013 from unprotected wireless networks. This company used Google’s Street View cars to steal data. While on the road, these cars retrieve data by scanning unprotected wireless networks. Thus, the company got emails and passwords without the owners’ consent. However, Google was fined $7 million for it.
Although the company did not use the hacking attack, it seems as the hackers usually do for stealing data. But the organization did not use Bluetooth for that violence. However, ensure that you must not keep turning on your Bluetooth because it can make the device vulnerable. However, hackers can have other intentions also. For example, Kidnappers and terrorists can use the hacking technique to hide their identities. As a result, it becomes challenging for authorities to trace them.
How Can You Prevent A Bluesnarfing Attack?
We have given here some ways to prevent the attack. However, this process is challenging as you can not file a data breach claim, and it is because no third parties are there. Therefore, you have to take precautions to keep your data protected as you are solely responsible for it.
These are the methods through which it is possible to prevent an attack.
Deactivate Your Bluetooth:
You don’t need to connect your devices to Bluetooth all the time. Instead, turn on Bluetooth when you need merely. Otherwise, hackers can gain access to your device. However, if you forget to turn it off or on, again and again, it is better to keep your device in non-discoverable mode instead.
Never Accept Pairing Requests From Unknown Contacts:
You must not take a pairing request from a source you don’t know or trust. Multiple hackers send an unsolicited contact card or urgent seeming file to access your device. If you connect the hacker’s connection mistakenly, they will get all of your data.
Don’t Hold Sensitive Information on A Bluetooth Device:
Try not to store your sensitive information on a Bluetooth-supported device. It will help you to prevent any potential damage you might suffer soon.
Have A Strong Password/PIN:
Ensure that your device has a strong password and PIN. If you have a Bluetooth-enabled device, you must have a strong password. Usually, changing passwords often helps to offer enough protection. But if you have robust basic password protocols, it will be better.
Require Approval For All Connects:
Ensure that your device is not connected automatically with any pairing requests from known or unknown contacts. When you implement Two-factor Authentication (2FA), it will provide better protection. As a result, all control will come into your hands taken from the hacker.
Mind Your Distance:
Distance is a factor you should remember for this type of hacking attack. If you are out of range from hackers’ devices, your device is safe. In addition, using a safeguard can help you ensure that you never initiate a pairing of your device in public.
Know Your Devices:
Hackers are waiting for opportunities. Besides, if your device is in the wrong place at the wrong time, the risk of attack increases. Therefore, you should keep the confidential data in devices that don’t support Bluetooth. In addition, you need to install all recent updates on your smartphone or laptop.
You should disable the Bluetooth connection to prevent any unauthorized access. Cyberattackers need to do something to work while they get an active connection. There are several devices vulnerable to cyber threats because of having no safeguard. This hacking attack is increasing for a lack of awareness among Bluetooth users. Therefore, people should know about the attack and learn how to protect the data.
You can easily disable the Bluetooth connection if you have an older device. But if you’re using a modern smartphone, you can find built-in authentication. Hackers can bypass the authentication easily and pair with target devices. It indicates that having the latest technology is not always the best. Sometimes, using older devices is lucrative.
The Bottom Line:
As the number of connected devices increases daily, the number of cyberattacks also rises. You should keep the Bluetooth powered off to safeguard from Bluesnarfing. As modern smartphones have default authentication, these attacks are increasing. However, having an old phone helps you a lot. Keep such phones in non-discoverable/hidden mode for more security. You must not accept Bluetooth pairing requests from any unknown devices. Using essential digital safeguards, you can remain safe.
Frequently Asked Questions:
- What is Bluesnarfing in network security?
It is a theft of information from a wireless device hackers get via a Bluetooth connection.
- What is the difference between bluejacking and Bluesnarfing?
Bluejacking transmits data to the target device only. But Bluesnarfing steals data using Bluetooth from the target device.
- Is Bluesnarfing easy?
It is a very easily implementable type of hacking. Victims don’t know what it is, and hackers get their required details, including emails, text messages, or contact lists. A cyberattacker should be present within at least 10 meters of you to make the attack happen.