Blog
How to Choose the Right Firewall for Your Network
Firewalls are the first line of defense against cyber attacks that can halt productivity, halt operations, and lead to costly data breaches. Purchasing and installing the proper firewall is crucial to your organization’s overall network security.
Consider several factors when choosing a firewall for your network. These factors range from basic functionality to advanced capabilities.
Scalability
As a business, you need to be able to scale your network with time. This is because scalability can help you avoid threats that could put a stop to your business’s operations. For example, a DDoS attack can target file transfer servers, which could cause your entire business to go down if it’s not protected. This would leave customers without access to your products and services, which can cause them to turn away from you.
A scalable firewall can avoid these attacks by limiting the number of users accessing specific applications. This is especially important for businesses that use a variety of different end-users. For example, a marketing team that needs to access YouTube may require different policies than teachers who need to stream videos for a lesson. This is a feature that many people overlook, but it’s a crucial piece of the puzzle when securing your organization against threats.
Middle-market companies often don’t have the in-house experience to select the proper firewall for their needs. This is why a managed security service provider can be so helpful to these types of organizations. In addition to choosing the proper hardware, they can provide the expertise to ensure the firewall is configured correctly and managed for optimum security performance. To do this, a proof of concept should be conducted to see how the next-generation firewall performs in your organization’s operational environment.
Threat Prevention
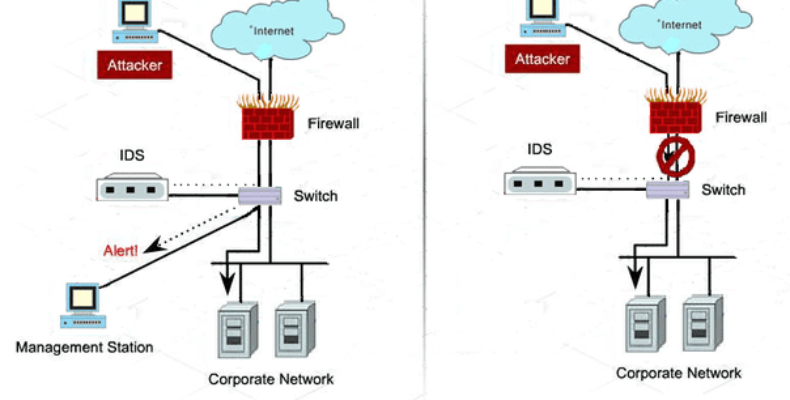
Firewalls can do more than detect cyber threats. They can also prevent attacks by blocking malicious packets before they reach your network. To do this, they must inspect the packets and determine, based on a set of rules, whether to allow or block them. The ability to inspect the packets and impose these rules is critical for your firewall to be an effective tool against sophisticated cyber threats.
If you’re looking for a strong firewall with advanced attack detection capabilities, look for one that can send real-time alarms to authorized personnel who can act on them. This will prevent a delay in response that might otherwise expose your data and systems to severe threats.
Having a powerful sandboxing feature is another essential capability to look for in a firewall. This will take suspicious files and executables off your network and open them in a controlled virtual environment to test their integrity. This can uncover hidden malicious code and help you avoid the risks of downloading dangerous files.
Your firewall should offer visibility and control across the entire network, including the cloud, data center, and remote users. It should be able to protect the business from escalating cyber dangers and provide security efficacy irrespective of where data is stored or who is accessing it. This is why it’s essential to involve all stakeholders when evaluating a firewall for your network.
Data Loss Prevention (DLP)
As employees use the internet to access business applications, data, and networks from home, coworking spaces, coffee shops, or anywhere else, your firewall must keep that traffic safe. That means ensuring no one can remove files from your internal servers, send them outside or communicate with external systems via USB ports, email, instant messaging, or other protocols. This requires DLP capabilities that identify and analyze sensitive information, classify it for protection policies, control removable devices like USBs, and prevent data loss to remote sites or outside vendors.
A good hardware firewall should come with an integrated DLP solution. A DLP feature can detect malware at the network level and then quarantine or block it from entering other systems on your internal networks. This can prevent cyber attacks, save your organization money and ensure the security of confidential business data.
The best firewall software should also include a robust, user-entity behavior analytics (UEBA) and threat modeling capability that allows it to identify risks and patterns of behaviors across your workforce. This can help your security team to fine-tune policies for maximum protection without hampering productivity. Finally, your chosen firewall should have a community of technology partners that can provide seamless integration with your infrastructure from both networking and security perspectives.
Endpoint Security
As a business, your bottom line is at risk with every breach. With attackers able to access your network from multiple points, including endpoint devices, implementing the proper firewall is essential to keep you safe.
Firewalls work at the packet layer, examining data packets that enter your system via the internet or other external connections and searching for malicious code or malware to infect your device and potentially spread across your network. A virus, worm, or Trojan horse can lead to unauthorized access, compromised systems, and the loss of vital information.
In addition to the features mentioned earlier, the best firewalls provide anti-virus and anti-spyware protection for each endpoint device. This prevents the spread of threats through email attachments, for example, and helps you eliminate threats before they become a significant problem.
When choosing the proper firewall for your network, the most important thing to remember is to consider all stakeholders and their needs. Networking teams, for example, want scalability, automation, and user application performance. Security professionals need a combination of security efficacy, scalability, and agility to keep up with the evolving threat landscape. Meanwhile, your employees need access to the tools they need to be as productive as possible. This often includes practices that render data access easier, such as bringing your device policies and remote working.